- Collecting Data is Easy, Analyzing It is Hard | Laserfiche Blog - And using it to gain better business results is harder still.
- Beware: 7 Sins of Cloud Computing | Innovation Insights | Wired.com
- Restaurants Turn Camera Shy - NYTimes.com
- Protecting information in the cloud - McKinsey Quarterly - Business Technology - Infrastructure - "Sophisticated IT shops are developing tools to map workloads to cloud-based hosting options using criteria like mission criticality, sensitivity of data, migration complexity, and peak processing requirements. This will make it possible for IT staff to pursue a mixed-cloud strategy and drive workloads to the hosting options that best balance risk and economic value ."
- Intel Slump Not a Problem – Death of BYOD Just Around the Corner | SiliconANGLE - I don't buy this. It seems the sort of trend (a la personal mobile phones) that is hard to imagine reversing itself.
- Roger Moore on Why Daniel Craig Is the Best James Bond Ever and What 007 Role He’s Dying to Play | TIME.com - "Yes, I thought Casino Royale was tremendous. I thought his action was quite extraordinary—he did more action in the first 30 seconds of the film than I did in 14 years of playing Bond. To me, he looks like a killer. He looks as though he knows what he’s doing. I look as though I might cheat at backgammon."
- It's Time to Cut Back on Social Media - Dorie Clark - Harvard Business Review - "It's become increasingly clear that with the proliferation of new platforms, no person or company can become the master of them all. Nor should they. The harder decision is figuring out which ones you should prioritize — or jettison."
- The states with the most data centers are also the most disaster-prone [maps] — Tech News and Analysis - "As GigaOM noted in its year-end cloud coverage, the solution to balancing cost and latency issues could come from prioritizing parts of the data load. Important data loads would direct to nearby centers, while less important data would go to cheaper—and/or safer—data centers far off. In the case of Sandy, with its 1,100-mile diameter, data centers in the middle of the country could keep companies online, even if their headquarters aren’t."
- http://www.eweek.com/security/hipaa-update-tightens-data-breach-liability-risks-for-it-companies/ - ""The majority of business associates now are probably not meeting the letter of the law in terms of their security obligations," Pollack told eWEEK. "I think it's going to require a wake-up call.""
- Aeolus Developer Conference: Deltacloud v1.0 | Aeolus Project Blog - Michal Fojtik gave an introductory presentation about Deltacloud v1.0 during the Aeolus Developer Conference.
- 2013: What happens in the cloud - Fortune Tech
Thursday, January 24, 2013
Links for 01-24-2012
Wednesday, January 23, 2013
Links for 01-23-2013
- Inventor Labs Blog - "What it's Really Like Working with Steve Jobs"
- Red Hat expands cloud management services | ZDNet - Red Hat had webcast further discussing ManageIQ acquisition (which has now closed) today. Piece by @sjvn here.
- The Panasonic Toughpad Press Conference - LOOK, ROBOT - "And now – music. Impossibly loud music that smashes out of speakers mounted on the stage and reverbs off the inside of my skull. Smoke floods the speaking platform in a move somewhere between inadvisable and ridiculous. Lights flash and spin around the room. I am defeated by the spectacle."
- 'Rogue clouds' giving IT staffs nightmares
- 3 reasons why “rogue clouds” are good — GigaOM Pro - .@mikekhusid @emorisse See also 3 reasons rogue clouds are good by @DavidLinthicum
- Three Backpacker-friendly Solar Chargers | Backpacker Magazine - @GeorgeDWatt @lovettjj Have not tried solar but I think it's improved
- A skeptic's review of the BioLite CampStove: it's neat but mostly impractical // Andrew Skurka - @GeorgeDWatt @lovettjj @mec I think I read something while back. Apparently not all that practical but does work
- How Low Could Apple Go? - Business Insider
Friday, January 18, 2013
Links for 01-18-2013
- If Dr. Seuss Books Were Titled According to Their...
- Protecting against cloud outages with Aeolus | Aeolus Project Blog
- New TPC Benchmark Compares Virtual Workloads - CIO.com
- Resiliency and reliability, the devil is in the details — Tech News and Analysis
- Devops, complexity and anti-fragility in IT: An introduction — Tech News and Analysis - "Reconciling the two views of the world means exploring three core concepts required to understand why a new IT model is emerging, but not necessarily replacing everything about the old model."
- The Art of Ofey: Richard Feynman's Sketches and Drawings | Brain Pickings
- ReadWrite – ReadWrite Survey Results: What A Typical BYOD Program Really Looks Like - In other words, use and pay for your own device if you like. "Companies pay for the BYOD devices at less than 10% of the companies responding. Workers and the company share costs at another quarter (27%) of responding organizations. Only 10% of companies buy the devices for their employees."
- Amazon Fails To Woo Developers - Business Insider - I didn't see this piece at time of AWS re:Invent. Talk about whiny and entitled
- American Malted Whiskeys Win Acclaim - NYTimes.com - Not much, that is, until last month, when a single-malt whiskey from the Balcones Distillery in Waco bested nine others, including storied Scottish names like the Balvenie and the Macallan, in a blind panel of British spirits experts.
- How to Upgrade Your MacBook Pro to an SSD | Mactuts+
- Branko's Thought Dump: On the state of Windows on the desktop - Pretty funny.
- 30 Linux Kernel Developers in 30 Weeks: Stephen Hemminger | Linux.com
- SPONSORED: The Taliban Is A Vibrant And Thriving Political Movement | The Onion - America's Finest News Source - Hilarious. Re: Atlantic “@mkapor: SPONSORED: The Taliban Is A Vibrant And Thriving Political Movement | The Onion ”
- Public Cloud Services Selection – 3 New Things — CIO Dashboard
- Fedora 18 is out and it’s Cloudy | The Cloud Evangelist - RT @EMEACloudGuy: #Fedora is out and it's Cloudy - heres my take and some tips
- If you lose your cellphone, don't blame Wayne Dobson - News - ReviewJournal.com - What a bizarre story.
- HP CEO Meg Whitman Counting on Executive Vice President John Hinshaw to Manage Corporate Costs - The CIO Report - WSJ - "Encouraged by the Salesforce.com implementation, Mr. Hinshaw has begun replacing other legacy software with cloud alternatives."
- The Minimum Viable Kitchen
- Expedia Rewards Warns Us of Unspecified Changes Coming Throughout 2013 - View from the Wing - "They even use my absolute least favorite word when referring to any loyalty program: enhance. I have almost never seen anything positive correlate with the use of that word. Memo to all loyalty marketing executives — whenever you actually do something positive, don’t call it an ‘enhancement’ because we won’t believe you — the word has been so abused by your colleagues to mask “taking away the things you care about most.”"
Wednesday, January 16, 2013
Podcast: The three audiences for enterprise Platform-as-a-Service
Listen to MP3 (0:13:28)
Listen to OGG (0:13:28)
Transcript:
Tuesday, January 15, 2013
Podcast: Cloud identity management with Ellen Newlands
- The changing security perimeter
- Interoperability and cross-donain trust in heterogeneous hybrid cloud environments
- The role of open standards in hybrid cloud identity management
- How to approach identity in the cloud
Listen to MP3 (0:11:40)
Listen to OGG (0:11:40)
Friday, January 11, 2013
Links for 01-11-2013
- SIGMA Aizu, Japan - YouTube - Nice Sigma promo video
- CRM and Cloud Computing To Grow Your Business - Salesforce.com - @DavidLinthicum It already has, especially if you consider the specialist platforms associated w and the like.
- Working On A Hosted Private Cloud Wave | Forrester Blogs
- How to Fold a Julia Fractal — Acko.net
- Can Meg Whitman Reverse Hewlett-Packard's Free Fall? - Businessweek
- I'm Jason Pontin, Editor in Chief and Publisher of MIT Technology Review, and This Is How I Work - "What do you listen to while you work? I absolutely cannot read or write with music playing. I'm suspicious of those who say they can."
- Why 2012 was the year of the e-single — paidContent
- The New Kingmakers, The Book – Available Now – tecosystems - RT @sogrady: new post | "The New Kingmakers, The Book - Available Now":
Recovering corrupt Lightroom catalogs
Back in December, something disconcerting happened. My Adobe Lightroom 4 catalog wouldn't load. Disconcerting because I had something on the order of 50,000 photos in that catalog and recreating the whole shooting match would be a frightful chore. Indeed, I wasn't even quite sure how frightful that chore would be.
However, I keep good backups in various forms and I was able to find a recent backup of my catalog that was happy enough to load. (The catalog does not include the photos themselves but it does include much of the information related to their organization and other metadata.)
But the problems didn't go away. And, today, even after a migration from a Windows system to a new Mac Mini, they came back in spades. I simply couldn't make a backup of a catalog from within Lightroom, which also refused to optimize it. I could pull in a somewhat earlier backup of the catalog through the Mac's Time Machine backup program, but there was obviously something deep wrong here. And Lightroom's repair catalog function refused to do anything useful.
As it turns out though, hat tip to Stephen Shankland for the info, Lightroom uses a SQLite3 database which has various tools one can use to fix corrupted databases.
The first thing I did was download SQLite3 and SQLite3_analyze.
SQLite3_analyze confirmed there was indeed some sort of problem. "database image is malformed" it told me. Some searching never did tell me what that means exactly but, in any case, it confirmed there was a problem with the database.
The real find came from Gerhard Strasse's blog. Read the blog but I just want to add a few comments.
Basically the steps are pretty simple.
First you dump the existing catalog into a text file as a bunch of SQL commands:
echo .dump | ./sqlite3 ~/lightroom_catalog.lrcat > ~/lightroom_catalog.sql
then, in theory, you can just suck that text into a new database file with:
./sqlite3 -init ~/lightroom_catalog.sql ~/lightroom_catalog_restore.lrcat
The blog notes that you may get an error or two (i.e. the duplicate keys or whatever that were causing the database issue) but it should work. It didn't in my case. (lightroom_catalog_restore.lrcat was a zero byte file on the first try.) The secret for me was at the end of the comments.
Reader Chairat Juengmongkolwong noted that if, after the first step, you go into the text file (lightroom_catalog.sql in this case) and replace the last line that says:
ROLLBACK; — due to errors
with the line:
COMMIT TRANSACTION;
And THEN do the
./sqlite3 -init ~/lightroom_catalog.sql ~/lightroom_catalog_restore.lrcat
it should work. Which it did for me. I never did see any errors so I'm not sure what the problem was. Hopefully, it is fixed now.
Obviously, if you've never touched a Unix/Linux command line this is probably a bit intimidating and you'll probably need to enlist some help. Make copies and work on backups! This process can doubtless be done on Windows as well although the details will be a bit different. The terminal console on a Mac is a Unix command line. I'd also note that if you have a very large catalog—mine is about 500MB—a lot of text editors won't be able to handle it. I ended up downloading and installing Vim which handled what a couple of others couldn't.
Another possible option, BTW, is to fire up a new catalog and import your existing (corrupt) catalog although this will cause you to lose any publishing services that you have setup and possibly other things as well. However, when I did this, it only imported a quarter or so of my photos. (Presumably it quit at the spot of the error.)
My configuration was a Mac Mini running Mountain Lion and Lightroom 4.3.
The one other thing I might add is that, given this is a fairly straightforward procedure, and one that is fairly standard for this particular SQLite database error as far as I can tell (whether for Lightroom or otherwise), it's unclear why it isn't embedded within Lightroom's own corrupt database recovery process.
Thursday, January 10, 2013
The possibilities of shorter books
In 2009, Philip Greenspun observed the following:
The pre-1990 commercial publishing world supported two lengths of manuscript:
1. the five-page magazine article, serving as filler among the ads
2. the book, with a minimum of 200 pages
Suppose that an idea merited 20 pages, no more and no less? A handful of long-copy magazines, such as the old New Yorker would print 20-page essays, but an author who wished his or her work to be distributed would generally be forced to cut it down to a meaningless 5-page magazine piece or add 180 pages of filler until it reached the minimum size to fit into the book distribution system.
What got me thinking about this again was the publication of my former colleague Stephen O'Grady's book, The New Kingmakers. (Grab a copy now. It's free. Really. Right now. I can wait. Back now? OK.)
It's relatively short at 50 pages but, as Stephen wrote me on twitter "between Race Against the Machine & the Kindle Singles model, i didn't see the point in stretching to meet artificial expectations." (Race Against the Machine is another recent non-fiction book by MIT's Andrew McAfee and Erik Brynjolfsson. It weighs in at 98 pages.)
For their part, Kindle Singles and other "e-singles" are apparently increasing in popularity. As noted in Laura Hazard Owen's post "Why 2012 was the year of the e-single":
In February, I reported that the company had sold two million Kindle Singles; as of September, that number was up to 3.5 million, and Amazon just expanded the program to the U.K., where it will include new entries by bestselling British authors as well as most of the American Kindle Singles.
And The New York Times generated lots of buzz with its beautifully executed "Snow Fall: The Avalanche at Tunnel Creek" feature.
That said, I expect the business models, especially when publishers are involved, will need some shaking out. Owen also noted that "With most Kindle Singles priced at $1.99, that’s only $7 million or so — and Amazon only takes 30 percent of it, making the revenue basically a rounding error." For conventionally published printed works, I suspect the economics will be even more challenging in most cases. Nonetheless, as e-books become ever more mainstream and reader/buyer expectations become less anchored by traditional publishing forms, I expect written works to start gravitating towards their natural lengths. (Although, realistically, as anyone who has been exposed to the endless over-length series in genre fiction will tell you, there will probably always be certain incentives to use more words rather than fewer.)
This discussion is especially pertinent to me because I'm in the process of wrapping up a book on cloud computing that I'll be publishing through Amazon's CreateSpace. I fussed around a fair bit regarding the "proper" minimum length for the book. At the end of the day, the book is going to hit a fairly conventional 60,000 word, 250 page or so length but it probably didn't need to. I don't really see anything in the book as filler, but I might have done some things differently if I weren't determined to hit a 50,000 word or so minimum target.
Wednesday, January 09, 2013
Links for 01-09-2012
- Twitter’s human-powered search is the present and future of AI — Tech News and Analysis
- Demystifying Cloud - "- Multi-hypervisor strategies are real and fueled by private cloud adoption - The public cloud constitutes the third most common hypervisor and must therefore be governed by the private cloud - Workload portability and cloud bursting are becoming more and more critical - Converged infrastructure is becoming more popular as a foundation for cloud"
- All computing isn’t equal: Here are the four types — Tech News and Analysis - Interesting cut at a taxonomy.
- Time To Stop Forgiving Cloud Providers for Repeated Failures | Andi Mann – Ubergeek - "While poorly run in-house IT abounds, I do know many enterprise IT shops that maintain better uptime than cloud service providers, and for very good reason. Cloud is immature as an IT discipline, and almost by definition embodies greater risk."
- (404) http://t.co/p0JN - RT @AndiMann: My new book "The Innovative #CIO" - tips, stories, examples & more on driving business+IT #innovation ...
- Houston, We Have Cloud | F5 DevCentral - "Despite the growing view that cloud security is a joint, shared responsibility between customer and provider, it is enterprise IT that must put into place the mechanisms for both controlling and proving control over data and access, not cloud providers or integrators. The provider can offer services designed to provide that control, but it is not the one that must implement the polices or report on their effectiveness."
- OpenShift PaaS Week in Review - January 6, 2012 | OpenShift by Red Hat - Here's a recap of all the great info that's been added recently to the #redhat #openshift blog
- Qualcomm's insane CES 2013 keynote in pictures and tweets | The Verge
- Amazon's Cloud Revenues, Examined - Cloud-computing - Infrastructure - Macquarie projected AWS 2013 revenues of $3.8 billion; 2014 revenues of $6.2 billion; and 2015 revenues of $8.8 billion, according to lead analyst Benjamin Schachter, who was cited by ZDNet in a report yesterday.
- 21 Emotions For Which There Are No English Words [Infographic] | Popular Science -
- Adobe Community: Recommendations for laptop specs to run CS2 and FrameMaker 8 - Adobe has pretty much screwed up wrt CS2 situation. They've put themselves in worst of 2 worlds
- Waving TDF Long Tail « The Document Foundation Blog - RT @florian_monfort: Guess who's biggest contributor to #libreoffice ?! Caolan Mcnamara from Red Hat!
Tuesday, January 08, 2013
Deploying and managing OpenShift Enterprise PaaS
We did a lot in the cloud computing space last year at Red Hat. We shipped our open hybrid cloud management software, CloudForms. We further ramped up our OpenStack activity with a technology preview. We acquired ManageIQ. We developed integrated cloud solutions based on the full Red Hat product portfolio.
But that's not all. One of the most exciting announcements of the past year was an on-premise version of Red Hat OpenShift Platform-as-a-Service. We'd been racking up new users and new applications—and expanding the functionality—on the hosted offering. The individual developers and IT departments who tried it out really liked the way they could develop using their choice of languages and frameworks and customize the development environment to meet their needs. Simply put, OpenShift Online (as it's now called) takes a lot of friction out of software development without limiting flexibility.
However, much as some customers appreciated the functionality of the online service, they wouldn't be able to make widespread use of it so long as it was only available in hosted form. To address these requirements, last November Red Hat introduced OpenShift Enterprise, an on-premise version of OpenShift PaaS. (For more background on enterprise PaaS, you can check out this whitepaper.)
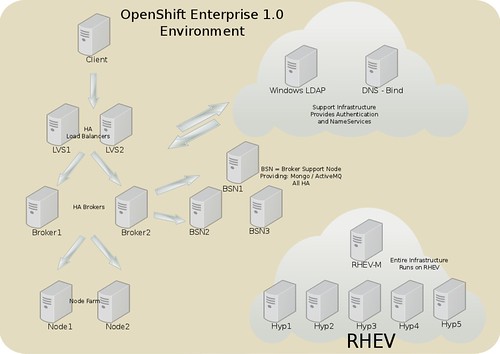
Unlike with a hosted service, an on-premise PaaS has to be deployed and managed. To assist with this process, Scott Collier and Steve Reichard on Red Hat's Systems Engineering team have put together a new reference architecture: "Deploying and Managing a Private PaaS with OpenShift Enterprise." The full reference architecture weighs in at almost 150 pages and includes lots of screen shots, configuration file entries, and command line text.*
The reference architecture shows how to deploy OpenShift Enterprise in a distributed way that separates domain name services, ActiveMQ, and MongoDB from the OpenShift Enterprise broker host. It also shows how to deploy both PHP and Java applications, enable applications with Jenkins continuous integration services, and use JBoss Developer Studio within an OpenShift Enterprise environment.
The broker is the single point of contact for all application management activities. It manages user logins, DNS, application state, and application orchestration. The broker can be communicated with programatically using a RESTful API or, alternatively, through a Web console, command line tools, or JBoss Developer Studio. ActiveMQ provides the messaging infrastructure for the broker. MongoDB provides the persistent data store. In the case of this reference architecture, the broker components were set up redundantly to provide high availability for OpenShift Enterprise's management system.
The reference architecture shows how to set up a load balancing cluster of OpenShift Enterprise brokers. The Load Balancing Add-on for Red Hat Enterprise Linux provides support for TCP load balancing independent of applications. It is composed of two major components: the Linux Virtual Server (LVS) and the Piranha Configuration Tool, a management tool with a GUI.
OpenShift applications run on nodes. Application multi-tenancy on each node is provided through SELinux and Cgroup restrictions that isolate each application's resources and data. Nodes can be added as required to provide the computing resources required by the applications running on an OpenShift Enterprise installation. The reference architecture demonstrates deploying the node software using the Red Hat Network (RHN) as well as Red Hat's content delivery network (CDN). This includes installing the Marionette Collective (MCollective) server orchestration framework packages on the node.
Gears are containers with a set of resources that allow users to run applications within a node. Districts define a set of node hosts and the resource definitions they must share in order to allow transparent migration of gears among hosts. They're not required but they're simple to use and any production installation can benefit from them. Districts allow a gear to keep its same ID when moved between any node hosts within the same district. Thus, users' apps will not be disrupted by changes when they are migrated between nodes even if they have hard-coded values.
There's a wealth of additional detail in the reference architecture but the above should give a high-level taste.
Increasingly, we see organizations looking to hybrid IT and hybrid cloud as detailed in this Gartner report. The addition of OpenShift Enterprise to our OpenShift Online service brings hybrid to PaaS. You don't need to choose. You can have both.
* The full configuration files are only available to Red Hat customers as part of the value-add of a Red Hat subscription.
Monday, January 07, 2013
State Street: Cloud isn't just a technology exercise
Over at Forbes, Joe McKendrick did a nice interview with Chris Perretta, the CIO of State Street, about the cloud computing initiatives going on there.
There's not a lot of detail about the technical aspects. What's there though are some nice insights into how State Street thinks about cloud computing and how they're using it to transform their business. A couple of excerpts:
We use cloud as a shorthand; it really is a complete view of the application delivery mechanism, the application frameworks that we use, and our ability to share real core components of our technology environment. A large chunk of what we do we write, and are realizing a lot of savings, efficiencies and capabilities in sharing new development frameworks across our enterprise, built into our cloud infrastructure. We can really move our development activities a lot faster than we have in the past. We’re also turbo charging our efforts to provide much more data insights for our customers, opposed to just top-level processing than we have done for them in the past.
A couple of things jump out for me. The first is that cloud isn't about plopping down some piece of technology. Rather, it's really about transforming enterprise IT. Common sense, perhaps, but I still find there's often too much focus on point products in cloud discussions. The second is the discussion around accelerating development. Everything I see suggests that, far from turning software into some kind of standardized utility, cloud computing seems to be ushering in what Gartner's Eric Knipp has called "a golden age of enterprise application development." (I discussed this trend in more detail last December.)
I think we’ll see the day where our cloud will be accessible to our clients — in fact, it is today. We’re building features here where customers actually load their data, and we keep data on their behalf. They can manipulate that data, they can join it, they can look at it in different ways, they can in essence write applications.
I'm not sure you could read a much more emphatic example of why you can't gain security just through defending the network perimeter. There is no inside and outside. Or, really, everyone's inside. Sharing happens pervasively. That's not to say there's no difference between a private cloud and a public cloud; indeed, State Street made a deliberate decision to build own cloud rather than using public cloud resources. But even if you've got a private cloud, you need to focus on things like multi-tenant security—which Red Hat's Matt Hicks has spoken and written about extensively.
I suggest reading the whole interview. It's not long but good stuff. State Street was a 2012 Red Hat Innovation Award winner for "OUTSTANDING OPEN SOURCE ARCHITECTURE: Recognition of a combination of Red Hat's platform, middleware, cloud and/or storage solutions to create innovative architectures based on Red Hat solutions."